Let me start off by saying, when it comes to securing your pool/servers, there is no magic pill or a silver bullet to the problem. You can only take these steps to safeguard your server and make it difficult for the attacker. Here are some (not all) of the steps taken to securing pool and the pledge.
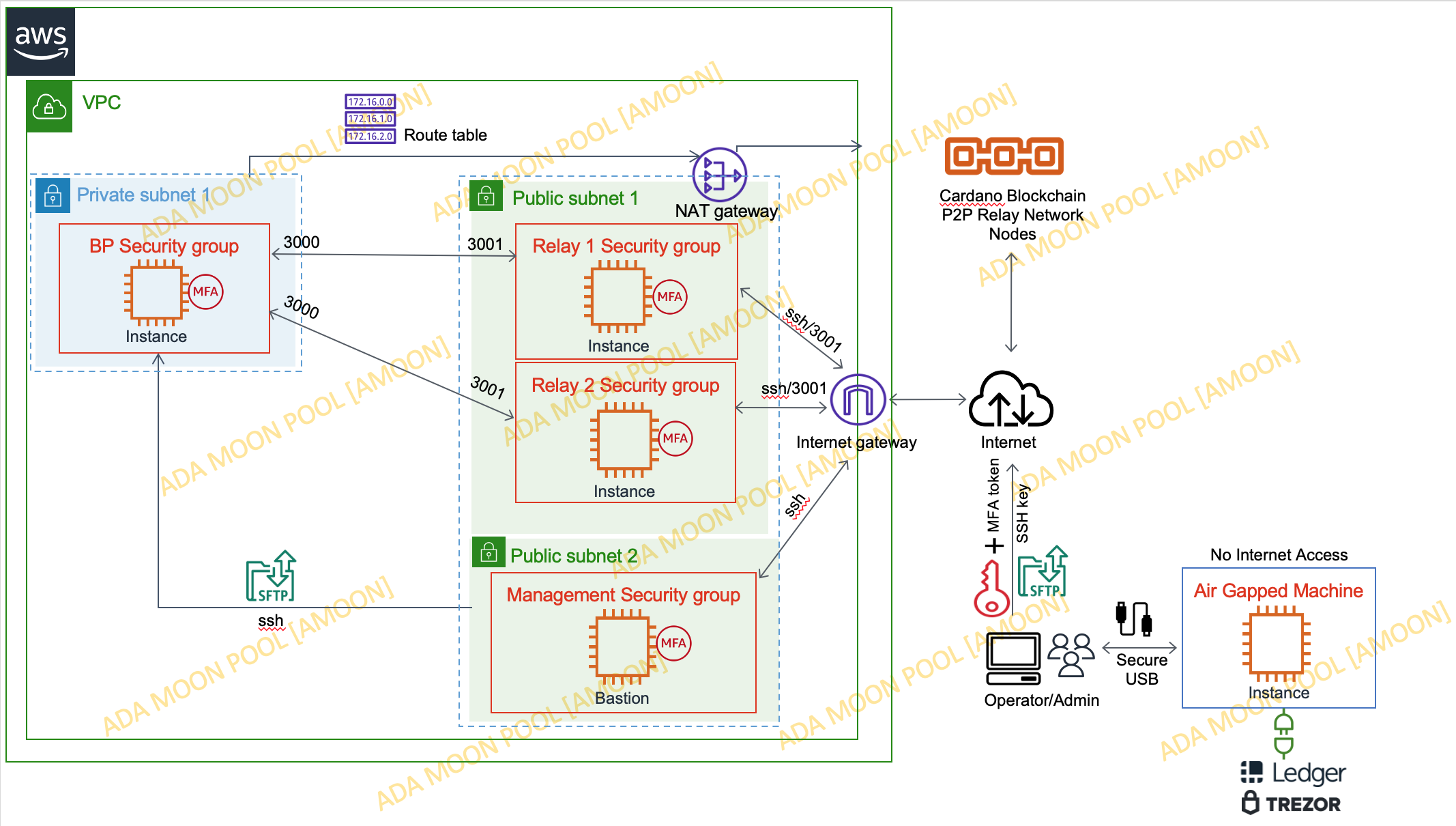
In this setup you will see 3 Subnets (2 Public and 1 Private subnet) and 4 Security Groups.
Management security group contains a bastion host, acts as a jumpbox to access producer nodes. This server is OFF mostly and is turned ON only on-demand, when we need to connect to the Block Producer node. When bastion is OFF, block producer is inaccessible to everyone (including us :-)).
Block Producer node runs in a private subnet with no internet access. It can only be accessed via Bastion Host (for Management). When Bastion is OFF, BP node is inaccessible, which provides an additional layer of security. And yes, it still runs and connected to relay nodes, updating transactions and slots. Even though this server doesn't have access to internet, it can still mint a block and do the leaderlog calculations.
Relay nodes are in public subnet with internet access, but protected by a firewall which only allows access to the relay port and ssh connection is restricted to specific IP.
Airgapped machine with no internet access, for offline transactions (cold keys are kept on this machine), also used to connect Hardware wallet to secure your pledge, for signing transactions, rotating KES keys and more.
© Farthest Inc. All Rights Reserved.